The first of these, Unauthorized Login Attempts is designed to let the Security Administrator - or whoever else has been given permission to use these applications - obtain details of suspicious log-ins to the system. You can click on "Unauthorized Login Attempts" to bring up the following filter:
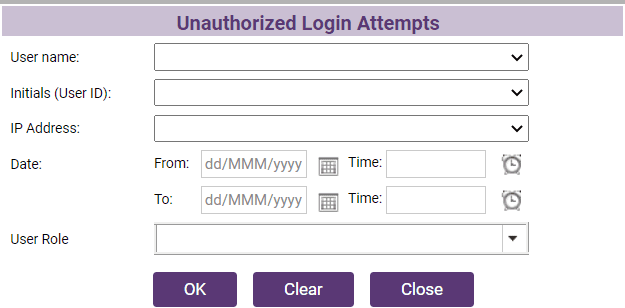
Complete the details for the person you think has had their ID misused and the system will produce a report of all log-ins supposedly done by that person for the period in question; if you don't know the IP address, or do not want to limit your search to one machine then leave this blank.